# ⚠️ Breaking Many deprecated queue config options are removed (actually, they should have been removed in 1.18/1.19). If you see the fatal message when starting Gitea: "Please update your app.ini to remove deprecated config options", please follow the error messages to remove these options from your app.ini. Example: ``` 2023/05/06 19:39:22 [E] Removed queue option: `[indexer].ISSUE_INDEXER_QUEUE_TYPE`. Use new options in `[queue.issue_indexer]` 2023/05/06 19:39:22 [E] Removed queue option: `[indexer].UPDATE_BUFFER_LEN`. Use new options in `[queue.issue_indexer]` 2023/05/06 19:39:22 [F] Please update your app.ini to remove deprecated config options ``` Many options in `[queue]` are are dropped, including: `WRAP_IF_NECESSARY`, `MAX_ATTEMPTS`, `TIMEOUT`, `WORKERS`, `BLOCK_TIMEOUT`, `BOOST_TIMEOUT`, `BOOST_WORKERS`, they can be removed from app.ini. # The problem The old queue package has some legacy problems: * complexity: I doubt few people could tell how it works. * maintainability: Too many channels and mutex/cond are mixed together, too many different structs/interfaces depends each other. * stability: due to the complexity & maintainability, sometimes there are strange bugs and difficult to debug, and some code doesn't have test (indeed some code is difficult to test because a lot of things are mixed together). * general applicability: although it is called "queue", its behavior is not a well-known queue. * scalability: it doesn't seem easy to make it work with a cluster without breaking its behaviors. It came from some very old code to "avoid breaking", however, its technical debt is too heavy now. It's a good time to introduce a better "queue" package. # The new queue package It keeps using old config and concept as much as possible. * It only contains two major kinds of concepts: * The "base queue": channel, levelqueue, redis * They have the same abstraction, the same interface, and they are tested by the same testing code. * The "WokerPoolQueue", it uses the "base queue" to provide "worker pool" function, calls the "handler" to process the data in the base queue. * The new code doesn't do "PushBack" * Think about a queue with many workers, the "PushBack" can't guarantee the order for re-queued unhandled items, so in new code it just does "normal push" * The new code doesn't do "pause/resume" * The "pause/resume" was designed to handle some handler's failure: eg: document indexer (elasticsearch) is down * If a queue is paused for long time, either the producers blocks or the new items are dropped. * The new code doesn't do such "pause/resume" trick, it's not a common queue's behavior and it doesn't help much. * If there are unhandled items, the "push" function just blocks for a few seconds and then re-queue them and retry. * The new code doesn't do "worker booster" * Gitea's queue's handlers are light functions, the cost is only the go-routine, so it doesn't make sense to "boost" them. * The new code only use "max worker number" to limit the concurrent workers. * The new "Push" never blocks forever * Instead of creating more and more blocking goroutines, return an error is more friendly to the server and to the end user. There are more details in code comments: eg: the "Flush" problem, the strange "code.index" hanging problem, the "immediate" queue problem. Almost ready for review. TODO: * [x] add some necessary comments during review * [x] add some more tests if necessary * [x] update documents and config options * [x] test max worker / active worker * [x] re-run the CI tasks to see whether any test is flaky * [x] improve the `handleOldLengthConfiguration` to provide more friendly messages * [x] fine tune default config values (eg: length?) ## Code coverage: 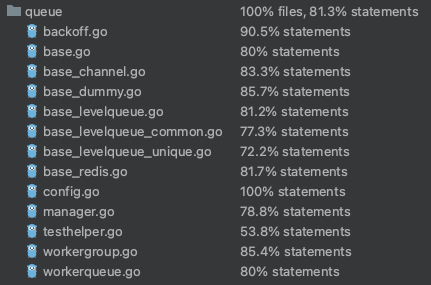
195 lines
6.4 KiB
Go
195 lines
6.4 KiB
Go
// Copyright 2017 The Gitea Authors. All rights reserved.
|
|
// SPDX-License-Identifier: MIT
|
|
|
|
package integration
|
|
|
|
import (
|
|
"net/http"
|
|
"net/url"
|
|
"testing"
|
|
|
|
auth_model "code.gitea.io/gitea/models/auth"
|
|
api "code.gitea.io/gitea/modules/structs"
|
|
"code.gitea.io/gitea/tests"
|
|
|
|
"github.com/stretchr/testify/assert"
|
|
)
|
|
|
|
func testAPIGetBranch(t *testing.T, branchName string, exists bool) {
|
|
token := getUserToken(t, "user2", auth_model.AccessTokenScopeRepo)
|
|
req := NewRequestf(t, "GET", "/api/v1/repos/user2/repo1/branches/%s?token=%s", branchName, token)
|
|
resp := MakeRequest(t, req, NoExpectedStatus)
|
|
if !exists {
|
|
assert.EqualValues(t, http.StatusNotFound, resp.Code)
|
|
return
|
|
}
|
|
assert.EqualValues(t, http.StatusOK, resp.Code)
|
|
var branch api.Branch
|
|
DecodeJSON(t, resp, &branch)
|
|
assert.EqualValues(t, branchName, branch.Name)
|
|
assert.True(t, branch.UserCanPush)
|
|
assert.True(t, branch.UserCanMerge)
|
|
}
|
|
|
|
func testAPIGetBranchProtection(t *testing.T, branchName string, expectedHTTPStatus int) {
|
|
token := getUserToken(t, "user2", auth_model.AccessTokenScopeRepo)
|
|
req := NewRequestf(t, "GET", "/api/v1/repos/user2/repo1/branch_protections/%s?token=%s", branchName, token)
|
|
resp := MakeRequest(t, req, expectedHTTPStatus)
|
|
|
|
if resp.Code == http.StatusOK {
|
|
var branchProtection api.BranchProtection
|
|
DecodeJSON(t, resp, &branchProtection)
|
|
assert.EqualValues(t, branchName, branchProtection.RuleName)
|
|
}
|
|
}
|
|
|
|
func testAPICreateBranchProtection(t *testing.T, branchName string, expectedHTTPStatus int) {
|
|
token := getUserToken(t, "user2", auth_model.AccessTokenScopeRepo)
|
|
req := NewRequestWithJSON(t, "POST", "/api/v1/repos/user2/repo1/branch_protections?token="+token, &api.BranchProtection{
|
|
RuleName: branchName,
|
|
})
|
|
resp := MakeRequest(t, req, expectedHTTPStatus)
|
|
|
|
if resp.Code == http.StatusCreated {
|
|
var branchProtection api.BranchProtection
|
|
DecodeJSON(t, resp, &branchProtection)
|
|
assert.EqualValues(t, branchName, branchProtection.RuleName)
|
|
}
|
|
}
|
|
|
|
func testAPIEditBranchProtection(t *testing.T, branchName string, body *api.BranchProtection, expectedHTTPStatus int) {
|
|
token := getUserToken(t, "user2", auth_model.AccessTokenScopeRepo)
|
|
req := NewRequestWithJSON(t, "PATCH", "/api/v1/repos/user2/repo1/branch_protections/"+branchName+"?token="+token, body)
|
|
resp := MakeRequest(t, req, expectedHTTPStatus)
|
|
|
|
if resp.Code == http.StatusOK {
|
|
var branchProtection api.BranchProtection
|
|
DecodeJSON(t, resp, &branchProtection)
|
|
assert.EqualValues(t, branchName, branchProtection.RuleName)
|
|
}
|
|
}
|
|
|
|
func testAPIDeleteBranchProtection(t *testing.T, branchName string, expectedHTTPStatus int) {
|
|
token := getUserToken(t, "user2", auth_model.AccessTokenScopeRepo)
|
|
req := NewRequestf(t, "DELETE", "/api/v1/repos/user2/repo1/branch_protections/%s?token=%s", branchName, token)
|
|
MakeRequest(t, req, expectedHTTPStatus)
|
|
}
|
|
|
|
func testAPIDeleteBranch(t *testing.T, branchName string, expectedHTTPStatus int) {
|
|
token := getUserToken(t, "user2", auth_model.AccessTokenScopeRepo)
|
|
req := NewRequestf(t, "DELETE", "/api/v1/repos/user2/repo1/branches/%s?token=%s", branchName, token)
|
|
MakeRequest(t, req, expectedHTTPStatus)
|
|
}
|
|
|
|
func TestAPIGetBranch(t *testing.T) {
|
|
defer tests.PrepareTestEnv(t)()
|
|
for _, test := range []struct {
|
|
BranchName string
|
|
Exists bool
|
|
}{
|
|
{"master", true},
|
|
{"master/doesnotexist", false},
|
|
{"feature/1", true},
|
|
{"feature/1/doesnotexist", false},
|
|
} {
|
|
testAPIGetBranch(t, test.BranchName, test.Exists)
|
|
}
|
|
}
|
|
|
|
func TestAPICreateBranch(t *testing.T) {
|
|
onGiteaRun(t, testAPICreateBranches)
|
|
}
|
|
|
|
func testAPICreateBranches(t *testing.T, giteaURL *url.URL) {
|
|
username := "user2"
|
|
ctx := NewAPITestContext(t, username, "my-noo-repo", auth_model.AccessTokenScopeRepo)
|
|
giteaURL.Path = ctx.GitPath()
|
|
|
|
t.Run("CreateRepo", doAPICreateRepository(ctx, false))
|
|
testCases := []struct {
|
|
OldBranch string
|
|
NewBranch string
|
|
ExpectedHTTPStatus int
|
|
}{
|
|
// Creating branch from default branch
|
|
{
|
|
OldBranch: "",
|
|
NewBranch: "new_branch_from_default_branch",
|
|
ExpectedHTTPStatus: http.StatusCreated,
|
|
},
|
|
// Creating branch from master
|
|
{
|
|
OldBranch: "master",
|
|
NewBranch: "new_branch_from_master_1",
|
|
ExpectedHTTPStatus: http.StatusCreated,
|
|
},
|
|
// Trying to create from master but already exists
|
|
{
|
|
OldBranch: "master",
|
|
NewBranch: "new_branch_from_master_1",
|
|
ExpectedHTTPStatus: http.StatusConflict,
|
|
},
|
|
// Trying to create from other branch (not default branch)
|
|
{
|
|
OldBranch: "new_branch_from_master_1",
|
|
NewBranch: "branch_2",
|
|
ExpectedHTTPStatus: http.StatusCreated,
|
|
},
|
|
// Trying to create from a branch which does not exist
|
|
{
|
|
OldBranch: "does_not_exist",
|
|
NewBranch: "new_branch_from_non_existent",
|
|
ExpectedHTTPStatus: http.StatusNotFound,
|
|
},
|
|
}
|
|
for _, test := range testCases {
|
|
session := ctx.Session
|
|
testAPICreateBranch(t, session, "user2", "my-noo-repo", test.OldBranch, test.NewBranch, test.ExpectedHTTPStatus)
|
|
}
|
|
}
|
|
|
|
func testAPICreateBranch(t testing.TB, session *TestSession, user, repo, oldBranch, newBranch string, status int) bool {
|
|
token := getTokenForLoggedInUser(t, session, auth_model.AccessTokenScopeRepo)
|
|
req := NewRequestWithJSON(t, "POST", "/api/v1/repos/"+user+"/"+repo+"/branches?token="+token, &api.CreateBranchRepoOption{
|
|
BranchName: newBranch,
|
|
OldBranchName: oldBranch,
|
|
})
|
|
resp := MakeRequest(t, req, status)
|
|
|
|
var branch api.Branch
|
|
DecodeJSON(t, resp, &branch)
|
|
|
|
if status == http.StatusCreated {
|
|
assert.EqualValues(t, newBranch, branch.Name)
|
|
}
|
|
|
|
return resp.Result().StatusCode == status
|
|
}
|
|
|
|
func TestAPIBranchProtection(t *testing.T) {
|
|
defer tests.PrepareTestEnv(t)()
|
|
|
|
// Branch protection on branch that not exist
|
|
testAPICreateBranchProtection(t, "master/doesnotexist", http.StatusCreated)
|
|
// Get branch protection on branch that exist but not branch protection
|
|
testAPIGetBranchProtection(t, "master", http.StatusNotFound)
|
|
|
|
testAPICreateBranchProtection(t, "master", http.StatusCreated)
|
|
// Can only create once
|
|
testAPICreateBranchProtection(t, "master", http.StatusForbidden)
|
|
|
|
// Can't delete a protected branch
|
|
testAPIDeleteBranch(t, "master", http.StatusForbidden)
|
|
|
|
testAPIGetBranchProtection(t, "master", http.StatusOK)
|
|
testAPIEditBranchProtection(t, "master", &api.BranchProtection{
|
|
EnablePush: true,
|
|
}, http.StatusOK)
|
|
|
|
testAPIDeleteBranchProtection(t, "master", http.StatusNoContent)
|
|
|
|
// Test branch deletion
|
|
testAPIDeleteBranch(t, "master", http.StatusForbidden)
|
|
testAPIDeleteBranch(t, "branch2", http.StatusNoContent)
|
|
}
|